Protect the Heart of Your Business: Why Information-Centric Security is Imperative for the Engineering Industry
The competitive advantage in mechanical engineering is based not only on powerful machine tools and assembly lines. The most valuable assets are information: unique 3D models, engine drawings, patented processing technologies, CNC algorithms, supply chain data for key components, strategic development plans, and trade secrets.
The traditional "perimeter" protection no longer works. Data is constantly moving: to contractors, to the cloud for collaborative development, to engineers' laptops, to the workshops of CNC machine operators. The risks are huge:
Key Risks
A direct threat to business survival
Leaking know-how to competitors or to the "black market" destroys multimillion-dollar investments in R&D and deprives you of uniqueness.
Huge financial losses
Fines for violating export controls (ITAR, EAR), contracts with OEM customers, intellectual property (IP) protection requirements. Recovery from an attack paralyzes production.
Reputational collapse
Loss of trust of key partners (car manufacturers, aircraft manufacturers) due to the compromise of their confidential data in joint projects.
An Information-Centric Security Model is a strategic response
It protects the information itself, wherever it is located:
-
Value Stamp: Your data (engine drawings, technical processes) are automatically labeled ("Strictly Confidential", "Trade Secret") depending on their criticality.
-
Protection follows the data: Security policies ("who can do what, when, and how with a file") are embedded in the data itself. Even if the file is copied to a USB stick or sent by mistake, access to it will be blocked or strictly controlled.
-
Control without barriers to work: Engineers will be able to safely collaborate with global teams and suppliers. Access to critical drawings can only be allowed for viewing in certain software by prohibiting copying or printing.
-
Protection from internal threats: Restriction of rights even for their employees — for example, the machine operator gets only the necessary CNC program, but not access to the entire database of design documentation.
-
Compliance with strict standards: Proof of control over export-controlled data (ITAR/EAR), protection of personal data of employees and partners, compliance with the requirements of contracts with government customers and OEM.
DCSM implementation is not an IT expense, but an investment in the sustainability and future of your business
This is the direct way:
- Preserve our unique competitive advantages and multimillion-dollar investments in development.
- Avoid catastrophic financial and reputational losses from leaks and cyber attacks.
- Safely scale innovation and global collaboration.
- Ensure the continuity of high-precision production.
In a world where data is the new currency of engineering, perimeter protection is outdated. Protect your own data. DCSM is a strategic necessity for industry leaders.
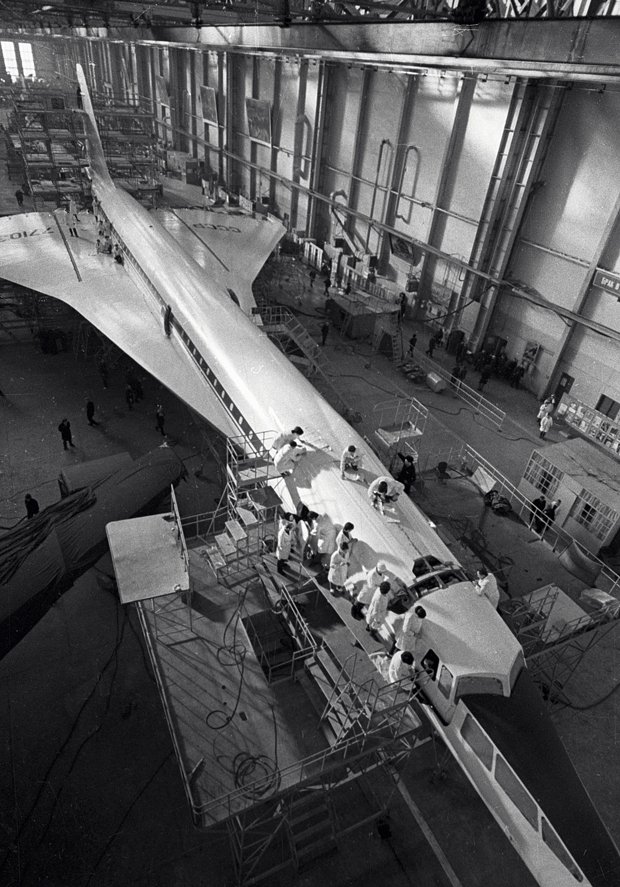
A. N. Tupolev, General Designer of the USSR Aviation Industry
